Sarah Rock, associate in the construction and projects department at law firm RPC, examines the draft text of the industry’s new guidelines on cyber threats, PAS 1192-5.
Earlier this month BSI released the draft PAS1192-5 for public review and comment, but what is it, what is it aiming to do and why do we need it?
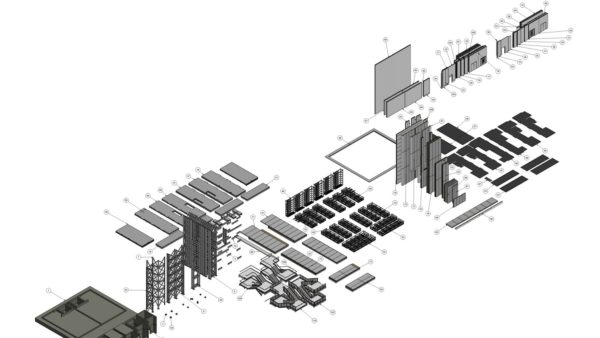
This latest Publically Available Specification (PAS) joins BS1192:2007, PAS1192-2, PAS1192-3 and BS1192-4 as one of the pillars of “BIM Level 2 wisdom”. These documents, alongside others such as the CIC BIM Protocol, set the standards for working to Level 2 BIM in the UK.
PAS1192-5 is stated to provide “a framework to assist asset owners and shareholders in understanding the key vulnerability issues and the nature of the controls required to enable the trustworthiness and security of digitally built assets”.
The document is not designed to hinder collaboration in the name of protecting sensitive data but rather to “ensure that information is being shared in a security minded fashion”. So the document addresses the need to be security-minded within BIM, in particular in relation to cyber security.
Cyber security is a means of protecting the cyber environment, which encompasses technology such as interconnected networks and computer based systems. BIM relies on the collaboration of data, often stored on a cloud or server (the Common Data Environment or CDE), between various users and so the policies and procedures in place across this process to protect the information in the model can be vital – anyone who has had their email or online bank account hacked can testify to the importance of cyber security.
The value of protecting detailed electronic information about the inner workings of a built asset, particularly one with sensitive security surrounding it, is obvious.
PAS1192-5 reviews the requirements for BIM and asset management and suggests procedures to be followed for each element. The document begins with an introduction and definitions to assist with the reader’s understanding. The PASs referred to above, as well as other documents, are directly referenced, making it clear that this PAS is not to be read as a standalone document: it looks to and requires understanding of the legislation and standards which came before it.
Read related articles
- New cyber security guidance for BIM and built assets published
- BIM bytes: Security of data under BS 1192-4:2014
- Cyber security threats trigger need for new PAS 1192-5
The document first looks at understanding the security context of the built asset. A holistic approach is recommended to the employer, encouraging them to appreciate the security needs relating to the people and processes involved, as well as that of the physical and technological security.
The next section gives a helpful “triage” process to assist in determining the security requirements for the specific built asset in question and whether or not it is “sensitive”. The triage process is well thought through and demonstrates that this document is not out to scare employers into employing additional consultants or commissioning lengthy and costly additional reviews and protocols. If the project has a certain level of sensitivity then certain protocols should be put in place, if it does not they are not required.
From my experience of working with employers on sensitive builds, the employer will be thinking about security risk and may well already have employed a security manager or another consultant to provide security policies. But further detail on the collaboration of the BIM team with the security manager, and how the security protocols can pass through the BIM team and process, would assist on a project with particular security risks.
Next comes guidance on developing a security strategy for a built asset which in turn is followed by advice on developing a built asset security management plan or “BASMP” (no BIM standard is complete without the obligatory new BIM acronym!).
The BASMP is to contain the security policies and procedures designed for the lifecycle of the built asset and so continue through into use of BIM during the facilities management phase.
The PAS continues by detailing a security breach management plan and what processes to put in place in case of a breach of cyber security, before going on to look at contractual measures in section nine. Here the employer is guided towards incorporating security requirements into the Employer’s Information Requirements (EIR) which will then dictate that the supply chain respond via the BIM Execution Plan (BEP). The EIR acts in the same way as an Employer’s Requirement document would in a design and build project, and likewise the BEP acts like the contractor’s proposals.
The final sections of the document cover application of security controls, monitoring and auditing of security controls, managing change and compliance with other legislation and standards.
Clause 5 of the CIC BIM Protocol should be viewed in light of PAS1192-5. Elements such as the integrity of electronic data and the risk of corruption of data are at risk of becoming floating obligations. On a sensitive build it seems prudent to allocate these risks and obligations specifically in order to ensure that all measures are taken for a secure CDE and protected sharing of information at the correct levels.
Whilst the PAS is aimed at employers, it is most likely to be read by the supply chain. For true collaboration in the area of cyber security, risk ought to be allocated fairly and appropriately and not leave the employer exposed.
PAS1192-5 gives a good grounding for cyber security. Collaboration between the security teams and the BIM teams on “at risk” projects is paramount in ensuring that the employer remains protected and the built asset remains secure.